The oil and gas business has become as much about bytes as barrels in recent years. Artificial intelligence, the internet of things (IoT), big data, and the ongoing digitization of the industry have not only made it a more-efficient machine but also a target to unscrupulous sorts looking to con-found, cash in, and move on. As more information comes forward regarding the May 2021 ransomware attack on Colonial Pipeline, it appears to have been a cash grab with the knock-on effect of physically crippling the company’s flow of fuel to East Coast states.
The outage was never the goal, but what it if had been? That question, or one similar, was part of what got the US Department of Homeland Security (DHS) involved and the subsequent announcement of a Security Directive that will require critical-pipeline owners and operators to report confirmed and potential cybersecurity incidents to the DHS Cybersecurity and Infrastructure Security Agency (CISA) and to designate a cybersecurity coordinator, to be available 24 hours a day, 7 days a week. It will also require critical-pipeline owners and operators to review their current practices as well as to identify any gaps and related remediation measures to address cyber-related risks and report the results to the Transportation Security Administration and CISA within 30 days.
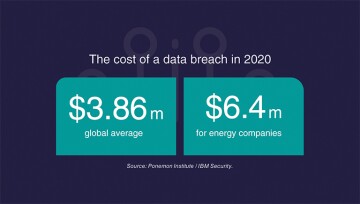
The bad guys made off with over $4 million in the Colonial attack; however, the US Department of Justice was able to recover about $2.3 million in the cryptocurrency paid by the pipeline operator.


